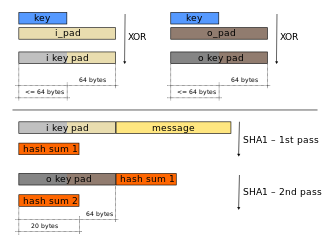
HMAC
| |||||||||||||||||||||||||||||||||||||||||||
Read other articles:
Milton FriedmanLahir(1912-07-31)31 Juli 1912Brooklyn, New YorkMeninggal16 November 2006(2006-11-16) (umur 94)San Francisco, CaliforniaKebangsaanAmericanInstitusiHoover Institution (1977–2006)University of Chicago (1946–77)Columbia University (1937–41, 1943–45, 1964–65)NBER (1937–40)BidangEconomicsMazhabChicago School of EconomicsAlma materColumbia University (Ph.D.), 1946, University of Chicago (M.A.), 1933 Rutgers University (B.A.), (1932)DipengaruhiAdam Smith, Irving ...

Raoul dari Lorraine Raoul (atau Rodolphe) dari Lorraine dikenal juga sebagai sang Pemberani (lahir 1320 dan meninggal 26 Agustus 1346, dalam pertempuran Crécy), putra adipati Ferry IV dari Lorraine dan Élisabeth dari Lorraine, merupakan adipati Lorraine dari 1329 hingga 1346. Setelah kematian ayahandanya, Raoul (Radulphus atau Rodolphe) baru berusia sembilan tahun. Dalam wasiat yang dibuat sebelum kematiannya, Elisabeth ditunjuk sebagai wali penguasa kadipaten hingga 1334.[1] Pernik...

Ichthyodes affinis Klasifikasi ilmiah Kerajaan: Animalia Filum: Arthropoda Kelas: Insecta Ordo: Coleoptera Famili: Cerambycidae Genus: Ichthyodes Spesies: Ichthyodes affinis Ichthyodes affinis adalah spesies kumbang tanduk panjang yang berasal dari famili Cerambycidae. Spesies ini juga merupakan bagian dari genus Ichthyodes, ordo Coleoptera, kelas Insecta, filum Arthropoda, dan kingdom Animalia. Larva kumbang ini biasanya mengebor ke dalam kayu dan dapat menyebabkan kerusakan pada batang kay...

Ini adalah nama Korea; marganya adalah Yoon. Yoon So-heeLahir7 Mei 1993 (umur 30)Busan, South KoreaPendidikanKAISTPekerjaanAktrisTahun aktif2013-sekarangAgenS.M. Culture & ContentsNama KoreaHangul윤소희 Hanja尹邵熙 Alih AksaraYun So-heeMcCune–ReischauerYun Sohŭi Templat:Korean membutuhkan parameter |hangul=. Yoon So-hee (Hangul: 윤소희; lahir pada 7 Mei 1993) merupakan aktris dari Korea Selatan Latar Belakang Yoon So-hee lahir di Stuttgart, Jerman p...

Часть серии статей о Холокосте Идеология и политика Расовая гигиена · Расовый антисемитизм · Нацистская расовая политика · Нюрнбергские расовые законы Шоа Лагеря смерти Белжец · Дахау · Майданек · Малый Тростенец · Маутхаузен ·&...

United States historic placeKendall Boiler and Tank Company BuildingU.S. Historic districtContributing property The Kendall Boiler and Tank Company Building is part of the larger Blake and Knowles Steam Pump Company National Register District.Show map of MassachusettsShow map of the United StatesLocation275 Third Street, Cambridge, MassachusettsCoordinates42°21′58″N 71°5′2″W / 42.36611°N 71.08389°W / 42.36611; -71.08389Part ofBlake and Knowles Steam Pump C...

Sarah LacySarah Lacy, diambil oleh Doc Searls di LeWeb3 di ParisLahir29 Desember 1975 (umur 48)Memphis, TennesseeAlmamaterRhodes CollegeSuami/istriGeoffrey Ellis Sarah Ruth Lacy (lahir December 29, 1975) adalah seorang penulis dan jurnalis teknologi Amerika Serikat.[1] Kehidupan awal Lacy menerima B.A. di bidang literatur dari Perguruan Tinggi Rhodes.[2] Karier Lacy merupakan mantan pembawa acara dari sebuah pertunjukkan video web Yahoo! Tech Ticker[3] dan merupa...

Lord Buddha statue in Japan Japanese sutra book open to the Shorter Sukhāvatīvyūha Sūtra Part of a series onMahāyāna Buddhism Teachings Bodhisattva Buddhahood Mind of Awakening Buddha-nature Skillful Means Transcendent Wisdom Transcendent Virtues Emptiness Two truths Consciousness-only Three bodies Three vehicles Non-abiding Nirvana One Vehicle Bodhisattva Precepts Bodhisattva vow Bodhisattva stages Pure Lands Luminous mind Dharani Three Turnings Buddhas and Bodhisattvas Shakyamuni Amit...

ACF FiorentinaCalcio Viola, Gigliati Segni distintivi Uniformi di gara Casa Trasferta Terza divisa Colori sociali Viola Simboli Giglio di Firenze Inno Canzone violaMarcello Manni(testo di Enzo Marcacci, riedita da Narciso Parigi) Dati societari Città Firenze Nazione Italia Confederazione UEFA Federazione FIGC Campionato Serie A Fondazione 1926 Rifondazione2002 Proprietario Rocco Commisso(attraverso Columbia Soccer Ventures LLC) Presidente Rocco Commisso Allenatore Vincenzo Italiano St...

Jalur kereta api Purwosari–Wonogiri–BaturetnoKonvoi militer di jalur kereta api Purwosari-Wonogiri–BaturetnoIkhtisarJenisJalur lintas cabangSistemJalur kereta api rel ringanStatusBeroperasi (segmen Purwosari–Wonogiri) Tidak Beroperasi (segmen Wonogiri - Baturetno)LokasiKota Surakarta, Kabupaten Sukoharjo, dan Kabupaten Wonogiri, Jawa TengahTerminusPurwosariWonogiriStasiun26OperasiDibangun olehSolosche Tramweg MaatschappijNederlands-Indische Spoorweg MaatschappijDibuka1892-1922PemilikD...

69th (South Lincolnshire) Regiment of FootActive10 December 1756–1 July 1881Country Kingdom of Great Britain (1756–1800) United Kingdom (1801–1881)Branch British ArmyTypeInfantrySizeOne battalion (two battalions 1795–1796 and 1803–1816)Garrison/HQMaindy Barracks, CardiffNickname(s)The Ups and DownsThe Old Agamemnons[1]EngagementsSeven Years' WarNapoleonic WarsFenian raidsMilitary unit The 69th (South Lincolnshire) Regiment of Foot was an infantry regiment of t...

2011 studio album by The Rural Alberta AdvantageDepartingStudio album by The Rural Alberta AdvantageReleasedMarch 1, 2011GenreIndie rock, Indie folkLabelPaper Bag Records (CAN)Saddle Creek Records (US)The Rural Alberta Advantage chronology Hometowns(2008) Departing(2011) Mended with Gold(2014) Departing is the second full-length album by Canadian indie rock band The Rural Alberta Advantage, released March 1, 2011 on Paper Bag Records in Canada and Saddle Creek Records in the United S...

Stringed musical instrument For the plant genus, see Valiha (plant). A valiha player in Ambohimahasoa, central Madagascar Lullaby played on valiha Valiha orchestra at the Paris World Exposition of 1931. Valiha with larger diameter bamboo tube. The valiha is a tube zither from Madagascar made from a species of local bamboo; it is considered the national instrument of Madagascar.[1] The term is also used to describe a number of related zithers of differing shapes and materials.[2 ...

National Historic Site of the United States Eleanor Roosevelt National Historic SiteStone CottageShow map of New YorkShow map of the United StatesLocationHaviland, Hyde Park, Dutchess County, New York, United StatesCoordinates41°45′47″N 73°53′56″W / 41.76306°N 73.89889°W / 41.76306; -73.89889Area181 acres (73 ha)EstablishedMay 27, 1977Visitors52,690 (in 2005)Governing bodyNational Park ServiceWebsiteEleanor Roosevelt National Historic Sit...

Scoot IATA ICAO Kode panggil TR[1] TGW SCOOTER Didirikan1 November 2011Mulai beroperasi4 Juni 2012PenghubungSingapura-ChangiKota fokusTaipei-TaoyuanProgram penumpang setiaKrisFlyerAliansiValue AllianceArmada59Tujuan70SloganGet Outta Here!Perusahaan indukSingapore AirlinesKantor pusat4 Airline RoadChangi AirportSingapore 819825Tokoh utamaCampbell Wilson (CEO)Karyawan1.976 (2020/21)Situs webflyscoot.com Scoot Tigerair Pte Ltd. (dioperasikan juga Scoot) adalah maskapai penerbangan bertar...

2015 UK local government election 2015 Canterbury City Council election[1] ← 2011 7 May 2015 2019 → All 39 seats in the Canterbury City Council20 seats needed for a majority First party Second party Party Conservative Labour Last election Conservative Seats won 31 3 Popular vote 29,670 16,954 Percentage 37.4% 21.4% Third party Fourth party Party Liberal Democrats UKIP Seats won 3 2 Popular vote 10,305 12,939 Pe...

الدوري التونسي لكرة اليد للرجال الموسم 1979-1980 البلد تونس المنظم الجامعة التونسية لكرة اليد النسخة 25 عدد الفرق 20 الفائز الترجي الرياضي التونسي الشبيبة الرياضية القيروانية (الثاني) الدوري التونسي لكرة اليد 1978–79 الدوري التونسي لكرة اليد 1980–81 تعديل مصدري - ت�...

Griffith InstituteHistoireFondation 1939CadreType InstitutPays Royaume-UniOrganisationSite web www.griffith.ox.ac.ukmodifier - modifier le code - modifier Wikidata Le Griffith Institute est une institution fondée dans le musée Ashmolean de l'université d'Oxford pour la promotion de l'égyptologie en tant que discipline. Il a été nommé d'après l'éminent égyptologue Francis Llewellyn Griffith, qui a légué des fonds dans son testament à la fondation de l'Institut. Il a été in...

Tool for separation of solid materials by particle size This article is about the tool. For other uses, see Sieve (disambiguation). Sift redirects here. For other uses, see Sift (disambiguation).Drainer redirects here. For the music culture, see Drain Gang. Metal laboratory sieves An ami shakushi, a Japanese ladle or scoop that may be used to remove small drops of batter during the frying of tempura ancient sieve A sieve, fine mesh strainer, or sift, is a tool used for separating wanted eleme...

Questa voce sull'argomento tennisti statunitensi è solo un abbozzo. Contribuisci a migliorarla secondo le convenzioni di Wikipedia. Mitchell KruegerMitchell Krueger nel 2022Nazionalità Stati Uniti Altezza188 cm Peso77 kg Tennis Carriera Singolare1 Vittorie/sconfitte 8-19 (29.63%) Titoli vinti 0 Miglior ranking 135º (18 luglio 2022) Ranking attuale ranking Risultati nei tornei del Grande Slam Australian Open 1T (2019) Roland Garros Q1 (2015, 2017, 2019) Wimbledo...